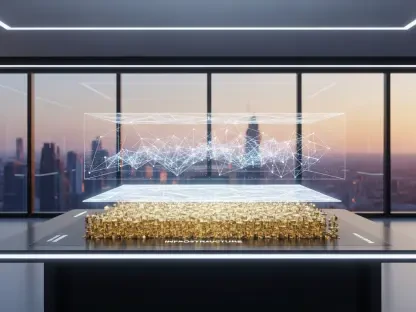
The rapid evolution of corporate digital infrastructure has left a massive trail of vulnerable data points that most executives are currently unaware of, creating a ticking time bomb for enterprise security protocols. While the migration from legacy, on-premises systems to decentralized Software-as-a-Service models promised unparalleled agility, it also dismantled the traditional perimeter-based security framework that once defined IT departments. Today, the modern enterprise functions across a vast, invisible web of applications, where data is generated and stored in silos that often bypass the rigorous scrutiny of centralized security teams. This architectural shift has created a protection gap that is no longer just a technical oversight but a fundamental business risk that threatens the continuity of global operations.
Central to this structural instability is the phenomenon of the shadow stack, a sprawling collection of specialized tools acquired by individual departments without the knowledge or approval of IT leadership. In an environment where a marketing director can subscribe to an automation platform or a legal team can implement a new filing system with a corporate credit card, the visibility of the organization’s total data footprint has vanished. As companies now find themselves managing hundreds of distinct applications, the challenge for the modern Chief Information Security Officer has transformed from defending a single fortress to securing an entire archipelago of third-party platforms.
The Structural Vulnerability of the Modern Enterprise SaaS Landscape
The decentralization of corporate data has fundamentally altered the power dynamics within the enterprise, shifting the weight of responsibility away from those best equipped to manage risk. When business functions move to the cloud, there is a recurring tendency to prioritize immediate accessibility over long-term durability. This fragmentation means that proprietary information is no longer stored in a cohesive, searchable database under the control of the organization but is instead scattered across various vendors, each with their own unique security standards and proprietary formats. Consequently, the ability to perform a comprehensive audit or enforce a universal security policy becomes nearly impossible as the number of platforms grows.
This lack of centralized oversight is particularly dangerous because it masks the true scale of an organization’s exposure. Research indicates that while many executives believe their critical data resides primarily in well-known platforms like Microsoft 365 or Salesforce, the reality is that the majority of business-critical information is often tucked away in less visible, specialized SaaS tools. These platforms may lack the sophisticated security features of larger providers, making them the weak links in the corporate chain. Without a unified strategy to inventory and protect these assets, the enterprise remains structurally vulnerable to both accidental loss and intentional disruption.
Analyzing the Shift in Global Data Threat Dynamics
Emergent Trends in SaaS-Targeted Cybercriminal Strategies
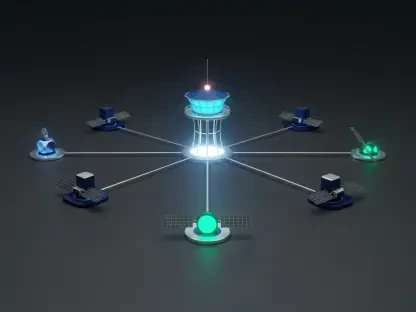
Cybercriminals have demonstrated a remarkable ability to adapt to the strengthening of traditional network defenses by pivoting their focus toward the largely unprotected SaaS ecosystem. As enterprises became more proficient at securing virtual machines and hardening local servers through immutability and air-gapping, the expected return on investment for traditional ransomware attacks began to decline. In response, malicious actors have targeted the cloud, recognizing that SaaS environments house the crown jewels of modern business, including sensitive customer records, proprietary source code, and confidential financial projections.
The strategic shift toward SaaS is driven by the density of value found within these platforms. A single successful breach of a development environment or a customer relationship management tool can provide an attacker with enough leverage to demand astronomical ransoms or facilitate sophisticated corporate espionage. Moreover, attackers have begun to exploit the inherent supply chain risks associated with cloud computing. By compromising a single SaaS vendor, they can potentially access the data of thousands of downstream customers simultaneously, turning a localized breach into a global crisis that spreads with terrifying efficiency.
Projected Growth and the Increasing Scale of Cloud-Based Information Risks
Looking forward from 2026, the volume of data stored within SaaS platforms is expected to climb at an exponential rate, further widening the gap between organizational exposure and executive perception. Market indicators suggest that as more industries adopt specialized cloud tools for everything from artificial intelligence training to supply chain logistics, the surface area for potential attacks will continue to expand. The risk is no longer confined to data theft; it now encompasses the total corruption of data integrity, where the goal of the attacker is to render the information unusable or untrustworthy, thereby crippling the victim’s ability to operate.
Performance metrics across the industry now indicate that a company’s resilience is increasingly defined by the speed at which it can recover data from isolated silos. As ransomware operators refine their techniques for encrypting cloud-based repositories, the traditional metrics of success, such as network uptime, are becoming less relevant. Instead, the focus has shifted toward data recoverability and the integrity of the backup copies. Without a fundamental change in how cloud data is preserved, the financial and reputational costs associated with data loss events will continue to rise, making SaaS protection a mandatory component of any long-term business strategy.
Deconstructing the Shared Responsibility Myth and Technical Limitations
A pervasive misunderstanding of the Shared Responsibility Model continues to be the most significant barrier to effective SaaS data protection. Many decision-makers operate under the assumption that by purchasing a subscription to a cloud service, they have also purchased a comprehensive insurance policy for their data. However, the fine print of nearly every major SaaS agreement clarifies that while the vendor is responsible for maintaining the infrastructure and ensuring the application is accessible, the customer remains entirely responsible for the data that resides within the system.
This distinction is often compared to a parking garage arrangement, where the owner of the facility ensures that the structure is safe and the gates function, but the owner of the vehicle is responsible for any items stolen from the interior. In the digital realm, if an employee accidentally deletes a critical database or if a malicious actor gains access to a tenant’s credentials and wipes out an entire project, the SaaS vendor is generally under no obligation to restore that data. Their primary concern is the health of the entire platform, and they often lack the tools to perform the granular, point-in-time recovery that a business would require to resume operations after a localized disaster.
Furthermore, the technical tools provided natively by SaaS vendors are often inadequate for true disaster recovery. Common features such as recycle bins or soft-delete windows offer a deceptive sense of security, as they are typically time-limited and integrated directly into the live environment. If a SaaS provider experiences a major system-wide outage or if an administrative account is compromised, these native tools become just as vulnerable as the primary data they were intended to protect. True resilience requires an independent, third-party backup solution that stores data in an immutable format, completely isolated from the vendor’s infrastructure.
Navigating the Complex Compliance and Security Mandates of Cloud Storage
The global regulatory landscape is becoming increasingly stringent, moving toward a model where organizations are held strictly accountable for data sovereignty regardless of the physical location of their servers. Laws governing privacy and industry-specific regulations now demand a level of control over data that standard SaaS configurations simply cannot provide. For an enterprise to remain compliant, it must demonstrate not only that its data is secure, but that it is retrievable and stored in accordance with regional mandates. This requirement has turned data protection from a technical preference into a legal necessity.
Compliance in the modern era hinges on the ability to maintain independent copies of data that can be audited and restored without relying on the primary service provider. As regulators increase their focus on operational resilience, the lack of a robust backup strategy is increasingly viewed as a failure of governance. Implementing advanced security measures, such as S3-compatible immutable storage, has become the gold standard for organizations that must protect themselves against unauthorized alterations and ensure that they can meet their legal obligations even in the event of a total platform failure.
The Future of Resilience Through Automated Data Sovereignty
The trajectory of the industry is clearly moving toward a model of active data ownership, where organizations take back the control they once yielded to third-party vendors. Emerging technologies are focusing on automated systems that can continuously scan and inventory the entire SaaS landscape in real-time, identifying new applications as they are introduced and automatically applying protection policies. This shift represents a move away from manual, reactive security toward a proactive stance where data is treated as the organization’s most valuable asset rather than an afterthought of the procurement process.
Future innovations in this space are directed toward enhancing offline recovery capabilities, ensuring that enterprises can export and utilize their data even if a SaaS vendor goes offline permanently or experiences a prolonged outage. This level of autonomy is essential for maintaining business continuity in an increasingly volatile digital economy. As cross-departmental governance becomes the norm, the integration of dedicated data protection leadership will ensure that security is woven into the fabric of every business decision, rather than being treated as a secondary concern for the IT department.
Bridging the Protection Gap Through Strategic Recovery Frameworks
The analysis of the SaaS landscape revealed that the reliance on vendor-provided security was a significant strategic error that many organizations committed during their initial transition to the cloud. It became evident that while the infrastructure could be outsourced, the ultimate responsibility for data integrity and business continuity remained an internal mandate. Leaders across the industry discovered that the most effective way to address the crisis was through the adoption of a rigorous recovery framework that prioritized the visibility of the entire shadow stack. By conducting thorough audits, companies identified the mission-critical applications that were previously operating without a safety net and integrated them into a centralized protection strategy.
The shift toward independent and immutable backup solutions proved to be a turning point in achieving true organizational resilience. These frameworks allowed businesses to bypass the limitations of native SaaS tools, providing them with the ability to restore specific, granular data points following a cyberattack or an accidental deletion. Looking forward, the emphasis moved toward maintaining a high level of data sovereignty, ensuring that information remained accessible and compliant with evolving global regulations. The final consensus among security professionals highlighted that the key to surviving the SaaS data protection crisis was the recognition that proactive recovery planning was the only way to safeguard an enterprise’s digital future.