The catastrophic collapse of the traditional network perimeter has forced a fundamental reckoning where the individual user is now the most volatile and vulnerable frontier in modern cybersecurity. In the current environment, the transition from centralized directories to highly distributed cloud architectures is no longer a strategic choice but a lived reality for every global enterprise. As the physical firewall fades into irrelevance, identity has emerged as the primary security perimeter, necessitating a radical shift in how organizations conceptualize and protect access. This perimeterless world demands a sophisticated understanding of the identity ecosystem, which currently comprises a sprawling web of Software-as-a-Service applications, cloud-native identity providers, and resilient but aging legacy on-premises systems.
Managing this complexity requires more than just technical integration; it involves analyzing the influence of dominant market players who are driving the industry toward integrated security platforms. These platforms seek to harmonize disparate signals from across the stack, yet the gap between centralized control and distributed execution remains a significant vulnerability. Security leaders are finding that traditional methods of siloed oversight are insufficient when a single employee might possess dozens of distinct accounts across various environments. The objective has shifted from merely managing logins to securing the specific person behind the myriad of accounts, ensuring that every digital interaction is verified and contextualized.
Market Dynamics and the Shift Toward Identity-Centric Defense
Emergent Trends in Unified Human Identity and AI Integration
The rapid integration of artificial intelligence into the modern workforce has fundamentally altered the digital identity footprint. AI assistants and autonomous agentic workflows now act as extensions of the human user, often possessing delegated authority to execute sensitive tasks across multiple platforms. This evolution in consumer behavior means the workforce no longer interacts with systems in a linear fashion; instead, they operate through a mesh of SaaS copilots and automated scripts that blur the lines of responsibility. Consequently, identity management must evolve from a focus on static accounts to a holistic, person-level visibility that accounts for these semi-autonomous actions.
Moreover, the delegated authority granted to AI tools creates a new layer of risk that traditional security models are ill-equipped to handle. When an agentic workflow is triggered, it often inherits the permissions of the user, yet the visibility into these sub-actions is frequently obscured. To address this, organizations are beginning to prioritize unified human identity frameworks that can track the intent and outcome of actions regardless of whether a human or an AI surrogate initiated them. This shift toward understanding the person as a singular point of risk represents the next phase of identity-centric defense.
Growth Projections and the Rising Demand for ITDR Solutions
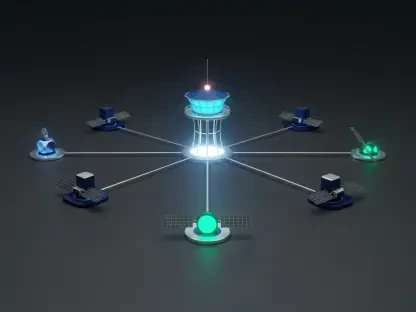
Current market data reveals a troubling reality where approximately 99% of cloud identities possess excessive permissions, many of which remain unused for extended periods. This imbalance has fueled a massive surge in demand for Identity Threat Detection and Response (ITDR) systems capable of identifying and neutralizing credential-based attacks in real time. Performance indicators for these systems are increasingly focused on their ability to correlate disparate data points and provide actionable intelligence before an attacker can move laterally. Projections suggest that the adoption of centralized identity correlation engines will become a standard requirement for enterprises by the end of the decade.
The growth of the ITDR market is also driven by the increasing sophistication of social engineering and credential harvesting techniques. As attackers focus on the path of least resistance, the ability to monitor behavioral anomalies across multiple cloud and on-premises environments becomes a critical differentiator. Forward-looking forecasts indicate that investment will continue to flow toward solutions that offer comprehensive visibility into “total effective access,” allowing security teams to see not just what permissions a user has, but what they can actually do within the context of the entire organization.
Overcoming the Complexities of Identity Fragmentation and Privilege Creep
Digital fragmentation has created significant security gaps, as disconnected control planes across hybrid environments prevent a unified view of risk. An employee might be offboarded from a primary directory but remain active in a secondary SaaS application, leaving a door open for potential exploitation. Navigating these risks requires more than just better tools; it requires a strategic overhaul of how digital personas are stitched together into a single virtual asset. By correlating these fragmented accounts, organizations can eliminate the blind spots that allow attackers to hide within the complexity of modern IT stacks.
The accumulation of unused permissions, often referred to as privilege creep, represents one of the most persistent threats to organizational integrity. As individuals change roles or take on temporary projects, their access rights tend to expand but rarely retract, leading to a bloated attack surface. Strategic solutions now focus on automating the reduction of these permissions through continuous monitoring and administrative oversight. Enhancing operational efficiency in this manner not only secures the environment but also reduces the manual burden on security teams during incident response, allowing them to focus on high-level strategy rather than account-level cleanup.
Navigating the Regulatory and Security Compliance Framework
Adherence to the Principle of Least Privilege (PoLP) has moved from a best practice to a cornerstone of modern regulatory standards. Data privacy laws increasingly demand that organizations maintain granular control over identity metadata and behavioral signals, ensuring that access is granted only when strictly necessary. Strengthening compliance now involves the implementation of “total effective access” audits, which provide a transparent view of the permissions landscape. These audits are essential for securing business-critical information against unauthorized lateral movement, which remains a primary goal of identity-driven breaches.
Furthermore, the intersection of identity and compliance requires a proactive approach to administrative oversight. Automated systems that flag deviations from established security policies allow organizations to maintain a continuous state of audit-readiness. This level of transparency is vital for protecting sensitive data and maintaining the trust of stakeholders in an era of increasing scrutiny. By aligning identity governance with regulatory requirements, businesses can create a resilient framework that protects both the individual and the enterprise from the legal and financial fallout of a security failure.
The Strategic Future of Identity Governance and Autonomous Security
Emerging technologies are currently being developed to provide real-time risk scoring and behavioral posture insights, allowing for a more dynamic response to potential threats. The rise of machine identities, which now often outnumber human users, represents a major potential market disruptor. Correlating these machine identities with their human owners or sponsors is becoming a critical task for ensuring accountability. Future growth areas will likely focus on AI-augmented digital environments where cross-platform identity stitching happens autonomously, reducing the window of opportunity for malicious actors.
Global economic shifts are also influencing cybersecurity investment priorities, with a clear move toward consolidation and efficiency. Organizations are seeking platforms that offer comprehensive protection rather than a collection of niche tools. This trend favors the development of autonomous security systems that can predict and mitigate risks based on historical patterns and real-time data. As the landscape continues to evolve, the ability to maintain a unified and transparent view of all identities will be the defining characteristic of a successful security strategy.
Strengthening Organizational Resilience Through Unified Identity Visibility
The implementation of a 360-degree umbrella profile for every employee and contractor provided a transformative shift in how organizational resilience was maintained. By synthesizing data from every corner of the tech stack, security leaders successfully closed the gap between perceived security controls and the real-world access available to users. This transparency was not merely a technical achievement but a strategic necessity that allowed for the rapid identification of identity-first attacks. The shift toward a unified human identity model ensured that the focus remained on the person, providing a clear narrative of activity that informed every aspect of the security posture.
Strategic recommendations for the future highlighted the necessity of maintaining this visibility as a core component of risk management. Organizations that prioritized the correlation of disparate digital accounts into a singular, manageable asset were better positioned to navigate the complexities of an AI-driven world. The necessity of transparency became a recurring theme, as the ability to see the person behind every account proved to be the most effective defense against modern threats. Ultimately, the transition to unified identities established a new standard for governance, ensuring that security remained robust even as the digital landscape continued its relentless expansion.