The pervasive assumption that data hosted within cloud ecosystems is inherently immune to loss or corruption remains one of the most significant operational blind spots for modern enterprises. While the shift to Software-as-a-Service (SaaS) platforms has undeniably streamlined workflows and reduced the burden of maintaining physical hardware, it has simultaneously introduced a layer of complacency regarding the stewardship of digital assets. Many business leaders operate under the dangerous illusion that the multi-billion-dollar infrastructure of providers like Microsoft, Google, or Salesforce serves as a comprehensive safety net for their proprietary information. However, this comfort is often misplaced, as these providers focus on the resiliency of their platforms rather than the preservation of the individual records created by their users.
The architectural reality of the cloud is governed by the Shared Responsibility Model, a framework that explicitly divides duties between the service provider and the customer. In this arrangement, the vendor ensures that the application remains functional and the servers stay powered on, but the legal and operational burden of protecting the data itself rests squarely on the shoulders of the organization. This means that if a disgruntled employee purges a critical database or if a sophisticated ransomware strain encrypts a suite of shared documents, the service provider is under no obligation to restore that specific information. Third-party backup solutions have transitioned from being optional luxuries to becoming essential components of the modern security stack, acting as the final line of defense against the diverse threats that inhabit the digital frontier.
Relying solely on native recycle bins or basic retention policies is a high-stakes gamble that frequently leads to permanent data loss. Most SaaS platforms offer only short-term versioning or “soft-delete” features that are designed for minor accidental errors rather than systematic recovery. These native tools often lack the depth required to satisfy strict regulatory audits or to facilitate the recovery of complex data relationships, such as those found in highly customized CRM environments. Understanding the limitations of these built-in features is the first step toward building a resilient data strategy that bridges the gap between simple service uptime and true enterprise-grade data recoverability.
Navigating the Hidden Vulnerabilities of the Shared Responsibility Model
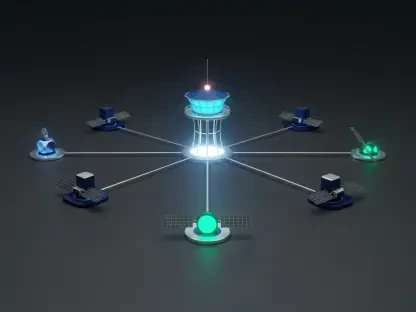
The conceptual divide in the Shared Responsibility Model often goes unnoticed until a crisis forces an organization to confront its own lack of preparation. Service providers are masters of “service availability,” ensuring that the platform is accessible to millions of users simultaneously. This is achieved through massive redundancy across data centers, but this redundancy is a double-edged sword; if a file is deleted or corrupted, that change is replicated instantly across the provider’s entire infrastructure. Without an independent, point-in-time backup, the “highly available” cloud merely ensures that your corrupted data is available everywhere at once, leaving the IT department with few options for a clean restoration.
Industry sentiment across the IT landscape suggests that the most common cause of SaaS data loss is not hardware failure but human error, ranging from simple mistakes to coordinated internal sabotage. Analysts and security researchers frequently point out that the ease of use inherent in SaaS applications also makes it incredibly easy to delete vast quantities of information with a few clicks. Furthermore, the rise of sophisticated phishing campaigns targeting global administrators means that an entire organization’s cloud presence can be compromised in a matter of minutes. Third-party backup solutions provide a necessary “air gap” by storing data in a separate security domain, ensuring that even if the primary cloud account is completely overtaken, a clean copy of the organization’s history remains safe and accessible for recovery.
Moreover, the lack of transparency in native retention policies can lead to a false sense of security that evaporates during a compliance audit. Many platforms have hidden “throttling” mechanisms or expiration dates on deleted items that are buried deep within service-level agreements. For instance, an administrator might assume that deleted emails are archived for years, only to find that they are purged after thirty days to save on storage costs for the provider. Leading backup software addresses this by offering immutable storage where data remains exactly as it was at the moment of backup, regardless of what happens in the live production environment. This proactive approach to data stewardship ensures that the digital legacy of a business is not subject to the shifting policies or technical limitations of a single third-party vendor.
The Evolution of Cloud Data Protection Strategies
The Critical Disconnect Between Service Availability and Data Recovery
Modern information technology departments frequently fall into the trap of conflating the operational status of a service with the integrity of the data it contains. A SaaS platform can boast “four nines” of uptime while an organization simultaneously loses access to months of financial records due to a synchronization error or a malicious script. This disconnect highlights a fundamental truth: availability is about the “now,” while recoverability is about the “then.” High-tier backup solutions like Barracuda Cloud-to-Cloud Backup are specifically engineered to address this by providing a historical record that exists independently of the live application’s state. By focusing on the Microsoft 365 ecosystem, Barracuda offers unlimited storage and retention, which provides a predictable cost model and a safety net that native Microsoft tools simply cannot match.
The transition from reactive storage to proactive protection has led to the development of tools that act as a “time machine” for corporate data. Professionals in the field emphasize that a reliable backup strategy must account for the “latency of discovery,” which is the time between when data is lost and when the loss is noticed. Often, a deleted file or a corrupted contact is not missed until weeks or months later, by which time the native recycle bin has been emptied. Software like IDrive Online and SaaS Backup caters to this need by offering a budget-friendly yet comprehensive shield for small businesses, allowing them to maintain long-term archives across a multitude of devices. This level of protection ensures that the size of an organization’s budget does not dictate the safety of its intellectual property.
Furthermore, the complexity of modern recovery requirements has rendered traditional “all-or-nothing” restores obsolete. In a fast-paced business environment, IT teams cannot afford to roll back an entire department’s mailbox to recover a single missing attachment, as this would result in a massive loss of productivity and the overwriting of legitimate new work. The consensus among technical architects is that the modern standard for recovery must include the ability to perform surgical restorations. This evolution is clearly visible in platforms like Cove Data Protection, which provides Managed Service Providers with the tools to manage diverse environments without the need for cumbersome server reboots or manual oversight, ensuring that the recovery process is as seamless and non-disruptive as possible.
Bridging the Gap Through Granular Restoration Capabilities
The ability to perform granular, object-level restoration is the hallmark of a sophisticated backup solution and is a primary differentiator from basic native tools. When a user deletes a specific row in a spreadsheet or a particular lead in a CRM, the goal of the IT department is to restore that specific piece of information without disturbing the surrounding data structure. This is particularly challenging in environments like Salesforce, where data points are connected by a web of complex relationships and metadata. Salesforce Backup & Recover stands out in this regard, as it is purpose-built to navigate these intricacies. It allows administrators to reconstruct not just the raw data, but the “context” of that data, ensuring that restored records retain their original links to accounts, opportunities, and tasks.
Leading analysts suggest that the metric of success for a backup tool is no longer just “can it restore,” but “how precisely can it restore.” This shift toward precision is driven by the need for operational continuity, where the goal is to get a single user back to work in minutes rather than hours. For instance, Acronis Cyber Protect Cloud integrates granular recovery with a unified security interface, allowing admins to search for specific files across all backed-up systems. This capability is vital during a security incident where only a portion of the data has been compromised, as it enables the business to isolate the damage and restore only what is necessary, thereby reducing the “blast radius” of the event and minimizing downtime.
Moreover, the move toward granular recovery has democratized data protection, making it accessible to non-technical users within an organization. Some modern solutions now feature “self-service” portals where employees can find and restore their own deleted emails or documents without opening a support ticket. This not only empowers the workforce but also relieves the IT department of the burden of handling minor recovery requests. By treating every individual file, email, and contact as a unique, recoverable object, these tools transform the backup from a dormant insurance policy into an active utility that supports the daily productivity of the entire enterprise.
Countering Modern Cyber Threats with Immutable Storage
The landscape of cyber threats has shifted dramatically, with ransomware groups now specifically targeting backup files to ensure that their victims have no choice but to pay the ransom. This “double extortion” tactic has forced the backup industry to innovate, leading to the widespread adoption of immutable storage. Immutability refers to a state where data, once written, cannot be modified or deleted for a set period, even by an administrator with full credentials. Keepit has gained significant traction by utilizing a blockchain-like architecture that creates a truly independent and immutable archive. This approach ensures that even if a global admin’s account is hijacked, the historical backups remain untouchable, providing a “gold copy” that is guaranteed to be clean and available for restoration.
Security professionals argue that a backup that can be deleted by the same credentials used to manage the primary application is not a backup at all; it is simply a redundant copy. To combat this, the best solutions employ “air-gapping” techniques, where the backup data is stored in a completely separate cloud infrastructure, often using different authentication protocols. SpinOne exemplifies this proactive stance by integrating ransomware detection directly into the backup process. If the software detects an unauthorized mass-encryption event occurring within a Google Workspace or Microsoft 365 account, it can automatically revoke the offending application’s access and immediately begin restoring the affected files from the last known good backup, often before the IT team is even aware of the breach.
Furthermore, the implementation of “Write Once, Read Many” (WORM) technology within SaaS backup tools has become a critical component of disaster recovery planning. This technology prevents any form of tampering, whether it originates from an external hacker or a disgruntled internal employee seeking to cause damage. By ensuring the integrity of the data at rest, organizations can meet the most stringent security certifications and demonstrate a level of resilience that is impossible to achieve with native cloud tools alone. As cyberattacks become more automated and persistent, the ability to rely on an unalterable record of truth becomes the most powerful weapon in an organization’s defensive arsenal.
Scaling Security and Compliance Across Diverse Ecosystems
For the modern enterprise, the challenge of data protection is no longer confined to a single application but spans a fragmented ecosystem of various SaaS platforms. Managing security and compliance across Microsoft 365, Salesforce, and Google Workspace simultaneously requires a unified approach that eliminates “security silos.” Druva Data Security Cloud has positioned itself as a leader in this space by offering a cloud-native platform that scales effortlessly into the enterprise tier. By centralizing policy management, Druva allows organizations to apply consistent data protection rules across their entire cloud footprint, ensuring that no application is left vulnerable due to a lack of oversight or a configuration error.
Compliance is another major driver for the adoption of third-party backup solutions, as regulations like GDPR, HIPAA, and CCPA require organizations to have strict control over their data’s lifecycle. The ability to prove that data is being backed up, stored in a specific geographic region, and purged according to legal requirements is a standard expectation for any global business. Advanced tools now offer “regional data sovereignty” features, allowing a company to ensure that its European data stays on servers within the European Union, while its American data remains in the United States. This level of control is often unavailable in the default configurations of major SaaS providers, making specialized backup software a necessity for maintaining legal standing.
Moreover, the trend toward “data governance” means that backup software is being used for more than just disaster recovery; it is becoming a tool for legal discovery and long-term archiving. IT leaders are increasingly looking for a “single pane of glass” that provides a comprehensive view of all protected data, complete with automated reporting and audit logs. This transparency is essential for passing rigorous industry audits and for demonstrating to stakeholders that the organization is a responsible steward of its information. By choosing a solution that integrates seamlessly with existing identity providers like Okta or Azure AD, businesses can ensure that their security policies are enforced consistently, regardless of where the data resides or how it is being accessed.
Implementing a Resilient SaaS Recovery Framework
To maximize the ROI of a SaaS backup investment, IT departments must transition from a “storage-centric” mindset to a “recovery-centric” framework. This involves recognizing that the mere existence of a backup does not guarantee a successful restoration; the value of the software is determined by the speed, accuracy, and reliability of the recovery process. Organizations should begin by conducting a comprehensive data audit to identify their most critical assets and determine their “Recovery Time Objectives” (RTO) and “Recovery Point Objectives” (RPO). This data-driven approach ensures that the chosen backup solution is configured to protect the right information at the right frequency, preventing the loss of vital business intelligence during a failure event.
A resilient recovery framework also requires the integration of automated testing and validation to ensure that backups are always “restore-ready.” The most common failure in disaster recovery is discovering that a backup is corrupted or incomplete only when it is needed most. High-quality tools like Cove Data Protection address this by offering automated recovery testing, where the software periodically performs a “dry run” of a restoration in a virtual environment. This process verifies the integrity of the data and provides a documented report of the successful test, giving administrators the confidence that they can meet their service-level agreements when a real crisis occurs.
Furthermore, the human element of the recovery process cannot be ignored, and the best frameworks prioritize simplicity and ease of use in their restoration workflows. During a high-pressure security incident, an administrator should not have to navigate a complex, command-line interface or wait for a slow support response to initiate a restore. Leading solutions focus on intuitive dashboards that allow for one-click recoveries and provide real-time status updates on the progress of the restoration. By reducing the technical friction of the recovery process, organizations can minimize the psychological stress on their IT teams and ensure a more rapid return to normal business operations.
Securing the Digital Frontier Through Proactive Data Stewardship
The shift to cloud-based applications has not diminished the importance of data protection; rather, it has transformed the nature of the tools and strategies required to maintain it. As organizations increasingly rely on SaaS platforms to manage their most sensitive information, the “Shared Responsibility Model” serves as a stark reminder that the ultimate accountability for data safety remains with the data owner. The evolution of the backup industry has kept pace with these challenges, delivering solutions that offer unparalleled granularity, immutability, and cross-platform management. Whether an organization is a small business looking for budget efficiency or a global enterprise requiring rigorous compliance controls, there is a tool designed to meet those specific needs.
Investing in a robust third-party backup ecosystem is no longer a matter of checking a box for the IT department; it is a fundamental act of proactive data stewardship. The digital history of a modern business is its most valuable asset, and leaving that asset vulnerable to the whims of a single cloud provider is a risk that few can afford to take. By embracing the principles of independence and recoverability, IT leaders can ensure that their organizations remain resilient in the face of accidental deletions, internal threats, and the ever-present shadow of cyber warfare. The “best” solution is ultimately the one that aligns with the specific risk profile and operational goals of the business, providing a solid foundation for growth in an increasingly volatile digital landscape.
In conclusion, the transition toward professional SaaS backup solutions represented a pivotal shift in how the industry approached data resilience. By moving away from the simplistic reliance on native cloud features, organizations successfully reclaimed control over their digital identities. The implementation of immutable storage and granular restoration capabilities effectively neutralized many of the most common threats that once paralyzed IT departments. This period of growth in the cloud sector was defined by the realization that data is only as secure as the independent recovery strategies protecting it. As a result, businesses that prioritized proactive stewardship found themselves better positioned to navigate the complexities of the modern digital economy, turning potential vulnerabilities into a cornerstone of their long-term operational success.