The rapid multiplication of digital threats has reached a staggering velocity where 3.2 new malicious entities emerge every single second, rendering traditional static defenses almost entirely obsolete. Cybersecurity experts now face a relentless onslaught of sophisticated programs that can rewrite their own logic to evade detection. This environment has necessitated a fundamental shift toward machine-learning frameworks that do not just react to known signatures but predict intent through behavioral patterns. By moving beyond simple pattern matching, these advanced systems analyze the underlying DNA of code to identify threats before they can execute.
Modern defense mechanisms must now integrate several layers of scrutiny into a single, cohesive workflow to maintain relevance in this fast-paced landscape. This technological evolution represents a move toward comprehensive platforms that handle everything from initial ingestion to deep forensic analysis. The goal is to provide a holistic view of the threat landscape, allowing security teams to understand the broader context of an attack rather than viewing individual incidents in isolation.
The Evolution of AI-Driven Threat Detection
Artificial intelligence has transitioned from a supplementary tool to the core engine of modern digital security. This shift was largely driven by the surge in AI-generated malware, which uses the same large language models and generative techniques as legitimate software to create polymorphic code. These malicious entities change their appearance with every new infection, making it impossible for legacy antivirus software to keep pace. Consequently, the industry has turned to neural networks that can generalize from past data to identify the subtle markers of malicious intent.
The context of this emergence is one of constant digital warfare where the speed of response is the most critical metric. Human analysts can no longer manually review every suspicious file, creating a bottleneck that attackers are eager to exploit. By automating the triage and classification process, AI-driven tools have restored a degree of balance to the field. This evolution ensures that defensive capabilities scale alongside the volume of data, providing a robust foundation for protecting critical infrastructure and private user information.
Core Pillars of Modern Malware Defense
The Maldive Detection and Analysis Pipeline: Precision Engineering
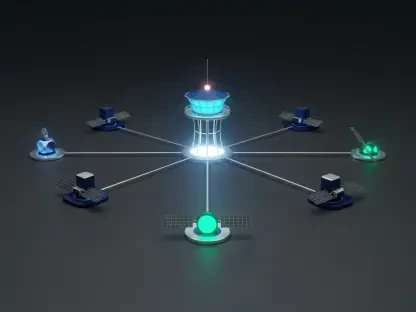
The Maldive project serves as a cornerstone of this new defensive architecture by integrating multiple layers of scrutiny into a single workflow. Its primary engine, the MalID module, orchestrates a combination of static code inspection and dynamic behavioral monitoring. By observing how a file interacts with a sandbox environment while simultaneously analyzing its mathematical structure, the system achieves a detection accuracy between 90% and 95%. This high precision does not come at the cost of speed, as the process typically completes in under sixty seconds.
Such efficiency is vital for maintaining the flow of enterprise traffic without compromising safety. The system does not merely flag a file; it generates a comprehensive behavioral profile that explains what the malware intends to do once inside a network. This deep insight allows for more effective remediation strategies, as security teams can see exactly which registries were targeted or which external servers the malware attempted to contact. It represents a significant leap from the “yes/no” binary of older detection methods.
Merlin: Adversarial Auditing via Reinforcement Learning
Conversely, the Merlin project focuses on the offensive side of system hardening through the use of reinforcement learning. This tool acts as an automated adversary that systematically modifies malware samples to find holes in existing security perimeters. By iteratively testing which structural changes can bypass a particular antivirus solution, it provides a rigorous benchmarking process. This ensures that defensive products are truly effective against the latest evasion techniques rather than relying on outdated marketing claims.
This proactive methodology, developed in partnership with HarfangLab, allows the Orange Group Security Division to make data-driven decisions regarding their security stack. It moves the conversation from theoretical protection to practical, tested resilience. By identifying exactly where a defensive model fails, developers can reinforce those specific weaknesses, creating a feedback loop that continuously improves the overall security posture. This adversarial approach is essential for staying one step ahead of professional cybercriminal organizations.
Innovations in Sovereign Code and Technical Independence
A defining characteristic of these advancements is the pivot toward sovereign code, which prioritizes technological self-sufficiency over reliance on third-party cloud platforms. By keeping the underlying algorithms and data storage within internal infrastructures, organizations mitigate the risks of data leakage and ensure that sensitive threat intelligence remains confidential. This strategy also facilitates a higher degree of customization, allowing developers to fine-tune AI models to the specific nuances of the malware targeting their unique sector.
Furthermore, there is a clear trend toward integrating fragmented security functions into unified, streamlined pipelines. In the past, detection, analysis, and reporting were often handled by disparate tools that did not communicate effectively. Modern sovereign platforms eliminate these silos, creating a single source of truth for security operations. This technical independence is not just about privacy; it is about the agility to update and deploy new defensive modules without waiting for a third-party vendor to provide a patch.
Real-World Applications in Telecommunications and Enterprise Security
Within the operations of the Orange Group Security Division, these technologies are utilized to manage the incredible volume of threats appearing across global networks. Central to this operation is the Malika database, a centralized repository that stores and categorizes malicious files to provide a unified source of intelligence. This repository allows different branches of the security team to access shared knowledge, turning isolated incidents into broader defensive strategies that protect millions of users across the telecommunications network.
The deployment of these systems has also revolutionized the auditing of commercial security products. By using the Merlin project to stress-test third-party tools, the organization can verify that the products they purchase are capable of stopping the most advanced threats. This real-world application proves that AI is not just a laboratory curiosity but a practical necessity for securing the vast, complex infrastructures that power modern society. It provides a level of oversight that was previously unattainable through manual testing.
Navigating the Obstacles of AI-Powered Defense
Despite the clear benefits, the implementation of AI-driven security is not without significant hurdles, particularly regarding the explainability of black-box models. Human analysts often find it difficult to trust a system that flags a file as malicious without providing a transparent reasoning for that classification. Building trust requires the development of “Explainable AI” (XAI) modules that can articulate the logic behind a decision in a way that a human expert can verify. This collaboration between machine speed and human intuition remains a top priority for ongoing research.
Another challenge involves the escalating arms race against generative AI threats. As attackers gain access to more powerful models, they can automate the creation of social engineering attacks and highly deceptive code. Current development efforts are focused on mitigating these limitations by refining the training sets used for defensive AI. Ensuring that models remain unbiased and resistant to adversarial poisoning is a continuous task that requires constant vigilance and frequent updates to the underlying data sets.
The Future Outlook for Adaptive Cybersecurity
The transition from laboratory prototypes to full-scale operational deployment marks a new chapter in the fight against digital crime. Automated threat simulation will likely become standard practice, allowing systems to autonomously patch vulnerabilities before they can be exploited by human attackers. This evolution suggests a global shift where security is no longer a bolt-on service but an intrinsic, self-evolving component of digital infrastructure. The focus is shifting toward systems that can learn and adapt in real-time to an ever-changing environment.
Technological independence will continue to play a pivotal role in shaping global security standards. As more organizations adopt sovereign code, the reliance on a few dominant tech giants will decrease, leading to a more diverse and resilient digital ecosystem. This decentralization of security intelligence makes it harder for attackers to find a single point of failure that can compromise an entire industry. The move toward proactive, AI-integrated auditing ensures that the bar for entry for cybercriminals remains prohibitively high.
Final Assessment of AI-Integrated Security Solutions
The integration of artificial intelligence into the cybersecurity landscape successfully moved the industry from a reactive posture to a proactive one. This review identified that while technical hurdles like model transparency persisted, the efficiency gains in detection and the robustness of adversarial testing provided a necessary shield against modern threats. The Maldive and Merlin projects demonstrated that when static, dynamic, and AI analyses are unified, the resulting defense is far greater than the sum of its parts. This approach proved to be a vital strategy for organizations dealing with high-volume, high-complexity data environments.
Ultimately, the adoption of sovereign, AI-driven pipelines established a new standard for data privacy and operational resilience that reshaped how large-scale enterprises defended their digital assets. The transition away from third-party dependence allowed for more agile responses to emerging threats and deeper customization of defensive tools. Moving forward, the industry must focus on refining these models to ensure long-term scalability and to build even greater trust between automated systems and the human experts who oversee them. The verdict is clear: AI-powered analysis is no longer optional for any entity operating in the modern digital age.