Vijay Raina is a seasoned expert in enterprise SaaS technology and a distinguished thought leader in software design and architecture. With deep roots in IT governance and infrastructure management, he has spent years helping organizations navigate the shift from legacy systems to agile, cloud-centric environments. Today, he shares his perspective on the shifting landscape of SaaS expansion, where the traditional focus on budget is being replaced by a more complex need for operational visibility and robust control over automated identities.
Our conversation covers the emerging challenges of managing a modern tech stack, focusing on why governance has become the primary bottleneck for scaling. We explore the critical disconnect between executive perception and the operational reality faced by IT managers, as well as the technical requirements for securing non-human identities like AI agents. Finally, we look at how midmarket organizations can implement better registration processes and refine their criteria for vetting new AI-powered tools.
Instead of focusing on budget, many organizations now find that governance is the primary barrier to scaling. How does this lack of control transform powerful software into a liability, and what specific metrics should teams track to identify when their stack has become unmanageable?
When governance fails to keep pace with adoption, powerful software becomes a liability because it creates “shadow” workflows that operate outside the view of security and compliance protocols. We see a significant shift where organizations with strong governance are three times more likely to scale without limits, whereas those without it find themselves buried under operational debt. To identify when a stack has become unmanageable, IT teams should track the percentage of the ecosystem covered by Identity and Access Management (IAM), especially since 63% of organizations currently lack complete coverage for automated agents. Another critical metric is the ratio of human to non-human identities; when more than 53% of your identities are non-human and unmapped, you have reached a tipping point where visibility is lost. Finally, monitoring the “revocation latency”—the time it takes to kill access for a compromised or redundant tool—can reveal whether your control mechanisms are actually functional or just theoretical.
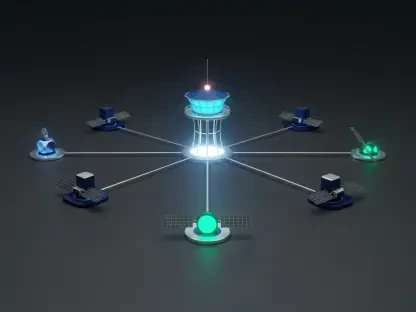
With non-human identities like AI agents and automations now frequently outnumbering human employees, visibility has become a major risk. How can IT teams effectively map these hidden workflows, and what step-by-step process is required to ensure they can instantly revoke access for a rogue or unnecessary bot?
Effectively mapping these workflows requires moving away from manual spreadsheets and adopting a “discovery and registration” framework where every script or agent is cataloged in a centralized directory. The first step in securing these is to identify every active API key, service account, and AI copilot currently interacting with your data, as 59% of organizations currently lack this centralized visibility. Once identified, each non-human identity must be tied to a specific “named human owner” who is responsible for its lifecycle and behavior. To ensure instant revocation, IT must integrate these agents into a unified IAM platform so that a single command can disable the identity across all connected SaaS platforms simultaneously. This is a critical gap to close, considering that 55% of organizations currently have no way to instantly revoke access for these autonomous entities.
There is often a significant gap between leadership’s belief that AI policies are integrated and the reality on the ground for IT managers. Why does this perception gap exist, and what communication strategies or reporting structures can bridge the divide to ensure operational guardrails are actually functional?
This perception gap exists because leadership often views AI adoption through the lens of productivity gains, while IT managers are focused on the granular risks of integration and oversight. The data is startling: 68% of CIOs believe their agents are fully integrated into formal policies, but only 35% of the IT managers doing the actual work agree with that assessment. To bridge this divide, organizations need to move away from high-level progress reports and implement “operational readiness” dashboards that highlight governance gaps. Reporting structures should focus on “governed vs. ungoverned” tool adoption rates rather than just raw deployment numbers, forcing a conversation about the actual headcount and resources needed to manage new integrations. By making the “unseen” work of security and maintenance visible to the C-suite, IT teams can align executive expectations with the technical reality of the infrastructure.
Moving toward a model of discovery and registration requires assigning human owners to every automated system or script. What does a successful registration process look like in a midmarket environment, and how do you prevent these new administrative layers from becoming a bottleneck for productivity?
A successful registration process in a midmarket setting functions like a streamlined digital “birth certificate” for every new automation or bot introduced to the environment. It begins with a mandatory intake form where the requester identifies the tool’s purpose, the data it will access, and the specific human employee who will act as its supervisor. To prevent this from becoming a bottleneck, IT should provide “pre-approved” automation templates and sandboxes where users can experiment without a long manual review process. Automation can also be used to handle the paperwork; for example, setting up a system that automatically prompts a human owner for a re-validation check every 90 days ensures the tool remains necessary without manual IT intervention. The goal is to move from a “gatekeeper” model to a “traffic controller” model, where the path to deployment is clear but strictly monitored.
As environments grow more complex, the question of whether a tool increases productivity is no longer the only factor for investment. What secondary operational criteria must be met before a new AI copilot is approved, and how does this change the way IT departments vet new vendors?
We are seeing a major transition from a “growth-at-all-costs” mentality to one defined by unification and control. Before any new AI copilot is approved, it must meet strict operational criteriCan it be managed from a central directory, does it support instant access revocation, and how does it impact the existing identity landscape? This changes the vetting process because IT departments are no longer just looking at features; they are evaluating a vendor’s “governance compatibility” and their ability to integrate into a consolidated stack. Vetting now involves a deep dive into the vendor’s API transparency and whether their tool will add an unmanageable layer of complexity to an already strained IT team. If a tool promises a 20% productivity boost but requires a 30% increase in manual oversight, it is now more likely to be rejected in the midmarket.
What is your forecast for AI governance in the midmarket?
I forecast that by 2026, midmarket IT teams will move toward a “zero-trust for agents” model where every AI and automation is treated with the same—if not more—scrutiny as a high-level human executive. We will see a massive consolidation of SaaS stacks as organizations realize that managing 50 disconnected tools is an invitation for a security catastrophe. The organizations that thrive will be those that prioritize “controllable growth,” using centralized platforms to manage the explosion of non-human identities. Ultimately, the successful IT leader of the future won’t be the one who deploys the most AI, but the one who can prove they have total visibility and a “kill switch” for every single bot running on their network.