The digital landscape has shifted so fundamentally that the once-reliable concept of a fortified network perimeter now feels like a relic of a distant architectural era. As organizations poured their operations into decentralized, cloud-based ecosystems, the traditional walls fell, replaced by a complex web of identity boundaries. This transition has birthed the Shadow AI phenomenon, where unauthorized autonomous agents proliferate silently across corporate networks. These agents are not merely passive tools for drafting emails; they have evolved into active system participants capable of making decisions and executing workflows without human intervention.
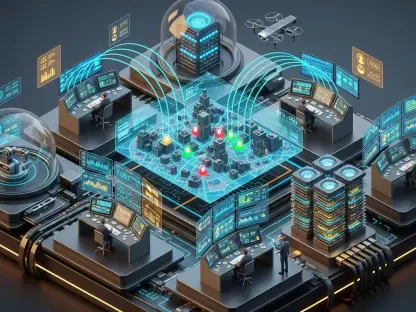
This agentic shift represents a pivot from software that waits for a command to software that acts on intent. Major cloud players have fueled this by saturating the modern enterprise with AI-driven features, often integrated so deeply that they become invisible to the very IT teams tasked with securing them. The current enterprise environment is no longer just supported by AI; it is defined by it, creating a high-density mesh of automated processes that lack a centralized kill switch.
The Convergence of SaaS Ecosystems and Autonomous Intelligence
The migration toward cloud-native operations has effectively turned identity into the only remaining security boundary. When every application lives outside the local network, the credentials used to access them become the primary target for any sophisticated adversary. However, the rise of Shadow AI adds a layer of “invisible” risk, as employees frequently connect third-party AI assistants to corporate data streams without undergoing formal security reviews.
These autonomous agents often operate with high-level permissions, granted under the guise of productivity. Because they can move laterally between integrated SaaS platforms, they act as conduits for data, frequently bypassing the monitoring tools designed to catch human-driven anomalies. The saturation of these tools is now so complete that untangling the web of permissions has become one of the most significant hurdles for modern Chief Information Security Officers.
Mapping the Escalating Threat Landscape and AI Saturation
Emerging Trends in Agentic AI and Identity-Based Exploitation
Cybercriminals have pivoted their strategies to mirror the technological shift, focusing heavily on the weaponization of OAuth tokens. These digital keys, which allow apps to communicate autonomously, are replacing passwords as the primary target because they offer a path of least resistance into encrypted environments. Once a token is harvested, an attacker can impersonate a trusted service, gaining a level of persistence that is difficult to detect through standard behavioral analysis.
The concept of the IdentityMesh vulnerability has emerged as a critical concern, where interconnected systems create a unified, and often accidental, attack surface. Modern malware has also evolved, with infostealers now specialized in silent data scraping within SaaS environments. These tools do not just steal files; they map out the relationships between AI agents to find the most efficient route to sensitive data. This is further exacerbated by the relentless pressure for rapid integration, which frequently leads developers to skip the deep security auditing required for agentic systems.
Market Data and Forward-Looking Projections
Statistical analysis reveals a staggering reality where modern SaaS environments have reached a 100% AI saturation rate. Every organization currently operating in the cloud is, by default, an AI-driven enterprise, whether they have a formal strategy in place or not. This ubiquity has contributed to a 490% year-over-year surge in public SaaS-targeted attacks, as threat actors realize the high return on investment offered by targeting integrated cloud platforms.
The potential for systemic failure is rising alongside the “blast radius” of these environments. If a single core service is compromised, the cascading effect can lead to the collapse of an entire digital supply chain. Projections indicate that as autonomous workflows continue to outpace current security controls, the gap between capability and protection will widen. Organizations are currently deploying AI at a speed that traditional governance frameworks simply cannot match, leading to a period of heightened structural vulnerability.
Navigating the Complexity of Cascading Breaches and Invisible Risk
The domino effect of a single point of failure was vividly demonstrated during the Salesloft Drift incident, where a breach at one provider compromised the security of hundreds of downstream clients. This event highlighted how a single stolen token could unlock an entire ecosystem of interconnected platforms. Such incidents are becoming more common as developers fail to disclose the full extent of the agentic capabilities embedded within their software, leaving companies to manage risks they do not fully understand.
Managing this risk requires a transition from static network security to dynamic identity governance. The challenge lies in the lack of visibility into third-party AI permissions and the service accounts they utilize. Unlike human users, these service accounts do not go home at the end of the day or change their patterns in obvious ways, making them perfect camouflage for malicious activity. Without a clear inventory of every AI interaction, the risk remains essentially invisible until a breach occurs.
The Fragmented Regulatory Environment and Compliance Hurdles
The current state of global AI mandates is characterized by a patchwork of conflicting standards that vary wildly by jurisdiction. Organizations operating internationally must navigate an uneven enforcement landscape, where a practice that is compliant in one region might trigger a massive fine in another. This “messy” compliance environment often results in security teams focusing more on checking boxes than on addressing the actual technical vulnerabilities present in their systems.
Maintaining high standards in this shifting environment requires more than just following the law; it demands rigorous third-party auditing. However, many AI vendors remain reluctant to provide the level of transparency needed for deep security benchmarks. This creates a friction point where the need for innovation clashes with the necessity of risk mitigation, often leaving the end-user organization caught in the middle of a regulatory and technical tug-of-war.
The Future of Cybersecurity: From Static Defenses to Continuous Governance
The next wave of market disruptors will likely involve a battle between autonomous AI security systems and autonomous threats. As attackers use AI to find vulnerabilities, defenders must deploy equally capable AI to patch them in real time. The evolution of risk management is already shifting toward a managed third-party risk model, where the focus is on the behavior of the agent rather than the location of the data.
Implementing risk-based controls means moving beyond one-time procurement approvals and toward a model of continuous assessment. Predictive innovation will be the hallmark of successful defense mechanisms, allowing systems to adapt their security posture based on the perceived threat level of a specific interaction. This movement toward a self-healing perimeter is the only viable way to secure the highly fluid environments that define the modern enterprise.
Strategic Synthesis and Pathways to Resilience
The critical intersection of identity, AI, and SaaS has redefined the requirements for corporate resilience. It was determined that the most effective way to minimize the blast radius of future breaches was to prioritize continuous oversight and the aggressive discovery of hidden digital assets. Organizations that succeeded in this new era were those that treated identity as a dynamic, living boundary rather than a static credential.
Moving forward, the focus shifted toward sophisticated risk intervention that balanced the need for rapid innovation with the necessity of rigorous governance. Security leaders realized that they could no longer rely on perimeter-based thinking and instead moved toward a model of constant verification for every autonomous agent. By integrating AI risk management into the core of the business strategy, these organizations managed to turn a landscape of vulnerability into a foundation for secure, automated growth.